In January of this year we reported on the potential rise of Cyber attacks on Industrial Control Systems and SCADA (ICS, SCADA and Ransomware). It is now being reported that ‘CrashOverride’, an attack vector that targeted the Ukraine electric grid last year, is now threatening Natural Gas and other infrastructure sectors across the globe. The National Cybersecurity and Communications Integration Center (NCCIC) is concerned, and is closely watching for any indication of this malware (Source: US-CERT June 12, 2017). As of today, the NCCIC risk rating for an attack in the US is Yellow (Medium).
The malware is active outside the US. It seems to focus on critical infrastructure organizations using ICS protocols in the electric power control systems: IEC101, IEC104, and IEC61850. However, US-based companies are warned not to get too complacent. CrashOverride could be strengthened without warning, and exploit existing protocols in the US through advancements in the attack vector.
Victims will experience a degradation of power grid reliability, denial of service to COM ports on devices, network mapping of the environment for propagation of the attack deeper into the enterprise, and requirement for manual reset of systems…not an easy task for many remote controls stations.
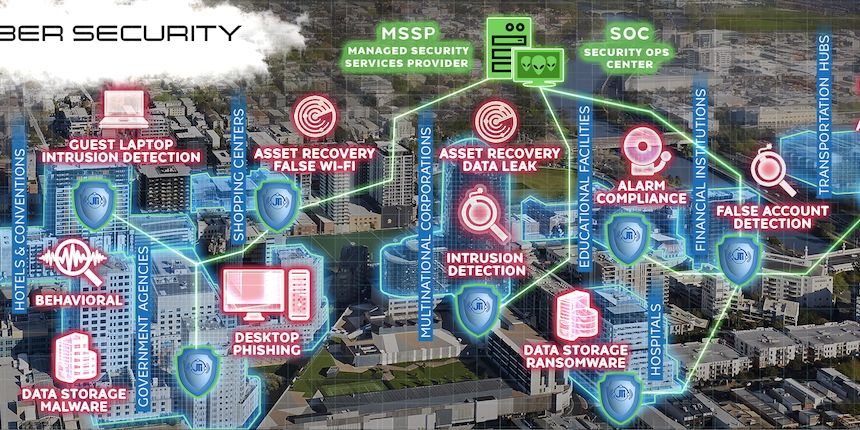
What is the solution? Layered cybersecurity defenses is a good start. Proper network hygiene which includes strong passwords, active monitored security, and closely management Role Based Access Controls would create a very serious barrier to penetrate the critical nodes of the network. Some Cyber Risk Management firms that deploy advanced managed security services with threat correlation services are generally able to detect these malware protocols.
All organizations in this industry are cautioned to remain vigilant! More will be reported as we get updates.
Please contact us for more information!