A DHS data breach was detected on May 2017 during a DHS Office of the Inspector General criminal investigation. A former employee had unauthorized access to a copy of the department’s case management system. The exposure was made public on January 3, 2018; a total of 246,167 federal government employees’ PII was stolen. The stolen data affects all employees who were part of OIG investigations from 2002-2014, the stolen data includes subjects, witnesses and complainants. It is unknown who the employee was that caused the breach.
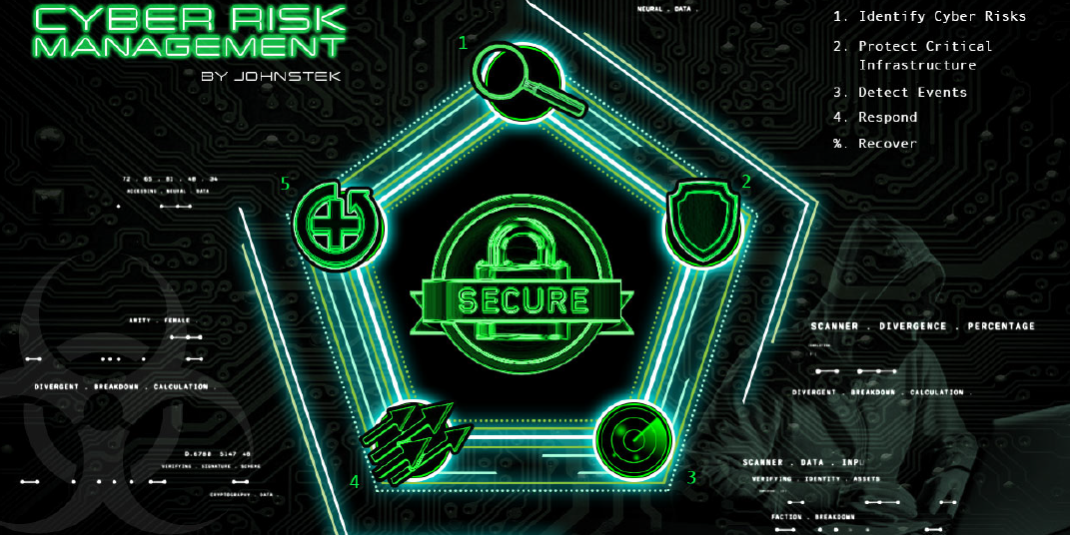
One lesson to learn from this, is any organization that closely follows a Cyber Risk Management Program that includes regular self-assessments using commonly accepted information security frameworks would have avoided such a breach. Access Management is one of the fundamental areas of technical control policy that would have assured that former employees no longer could gain access to active accounts on the enterprise.
The DHS launched a privacy investigation that included an evaluation, a forensic analysis, and a comprehensive assessment which aimed to analyze the risk that the affected individuals might face. The DHS commented that the “privacy incident” was not a cyberattack and that the stolen Personally Identifiable Information (PII) did not seem to be the goal of the breach. The PII that was obtained had names, Social Security numbers, dates of birth, positions, pay grades and duty stations of DHS employees. It also compromised the OIG by stealing the names, Social Security numbers, dates of birth, alien registration numbers, among many other types of sensitive information. The DHS is giving the people affected by the breach free identity protection and credit-monitoring services for 18 months.
They also said they are taking steps to better improve their network security like placing additional limitations on who have access to the case management system. They also are adding additional network controls to better identify unusual access patterns and will also perform a 360-degree review of DHS OIG’s development practices related to the case management system. The vulnerability exploited would have never existed had the IT team responsible for giving read/write access to the right people done their job. Giving access to sensitive information to the wrong person could devastate any agency. When someone has unnecessary access to private information it could potentially ruin many lives and that’s something it can’t be easily fixed assuming it can be fixed.
References
https://www.cnet.com/news/homeland-security-breach-exposes-data-on-240000-employees/
https://www.bleepingcomputer.com/news/security/department-of-homeland-security-suffers-data-breach/